Recently, X-Sec Labs caught a downloader which can download CoinMiner from a Http File Server(HFS).
First, let’s load it into Exeinfo PE.
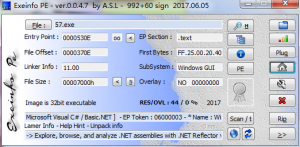 It’s clear that the file is written in .NET, so we can load it into decompiler.
It’s clear that the file is written in .NET, so we can load it into decompiler.
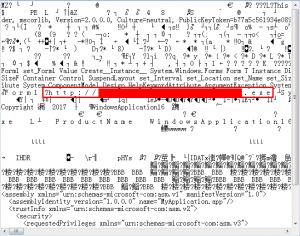
 Oh, the author did something to let the decompiler can’t decompile the core function!
Oh, the author did something to let the decompiler can’t decompile the core function!
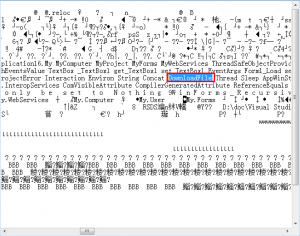
But we can open it with NotePad 😉
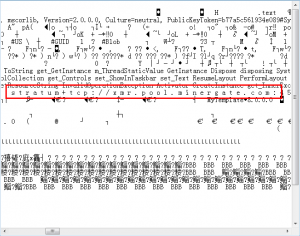 From these three images, we can guess the core function will download a file from specific URL, then run it with extra arguments. The extra arguments are usually used by CoinMiner to set specific mining pool & related account.
From these three images, we can guess the core function will download a file from specific URL, then run it with extra arguments. The extra arguments are usually used by CoinMiner to set specific mining pool & related account.
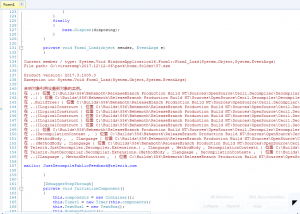
Now, we can manually download related file.
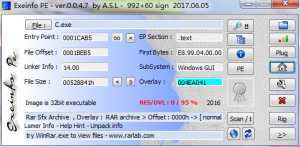 It’s a Rar Sfx Archive, we can view it through WinRAR.
It’s a Rar Sfx Archive, we can view it through WinRAR.
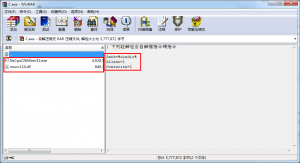 From the image we can see this Sfx Archive will drop files inside into Windows directory silently, files inside are commonly used CoinMiner.
From the image we can see this Sfx Archive will drop files inside into Windows directory silently, files inside are commonly used CoinMiner.
Related MD5:
2D28095E46B0241CE097E0860CED3593
F7E71A28F275A8C8B183181A647C2663
X-Sec Antivirus Detection:
Cloud Engine: Cloud:Trojan.Win32.CoinMiner(For downloader and downloaded file)
Local Engine: Trojan.Win32.CoinMiner.Ah(Only for downloader)
Required Virus Definition Version: 2017.12.07.01(Not released when this blog posted)