From July to now, we have collected lots of Chinese backdoor samples from a special source.
Sometimes they are encrypted, so they need a loader to download & decrypt.
We’re very lucky to get the full source code of this family of backdoor(Including source code, server module, client module and payload builder), so it’s easier for us to create signature.
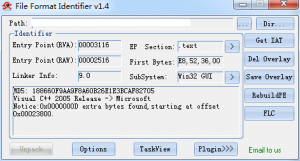
Here is a downloader sample.
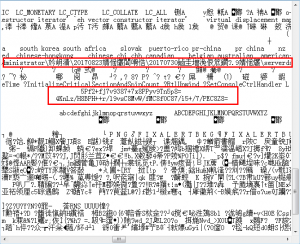
Seems that the file is not packed, let’s open it with Notepad 😉
It’s clear that we have found two interesting things, the first one seems like a PDB path(path contains Chinese), the other one is something encoded with base64.
Finally we found this:
If you just decode the string with base64, you will only see a messy code.
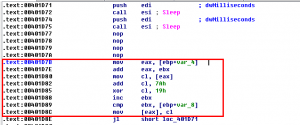
The downloader will decrypt URL from strings embedded, download the encrypted payload(in this case, the downloaded payload just need a string reverse), decrypt & load them into memory then run the code.
Related MD5: 188660F9AA9F8A60B26E1E3BCAF82705
X-Sec Antivirus Detection:
Cloud Engine: Cloud:Trojan.Win32.Downloader
Local Engine: Trojan.Win32.Crypted.Av!GEN
Required Virus Definition Version: 2017.09.24.01(Not released when this blog posted)